Turn usage into safe optimisation decisions.
CloudKnife identifies rightsizing, waste, and scheduling opportunities and explains the evidence behind each recommendation,so teams can approve changes with confidence.
Recommendations with evidence attached
A technical view built for review: impact, risk, confidence, and the “why”.
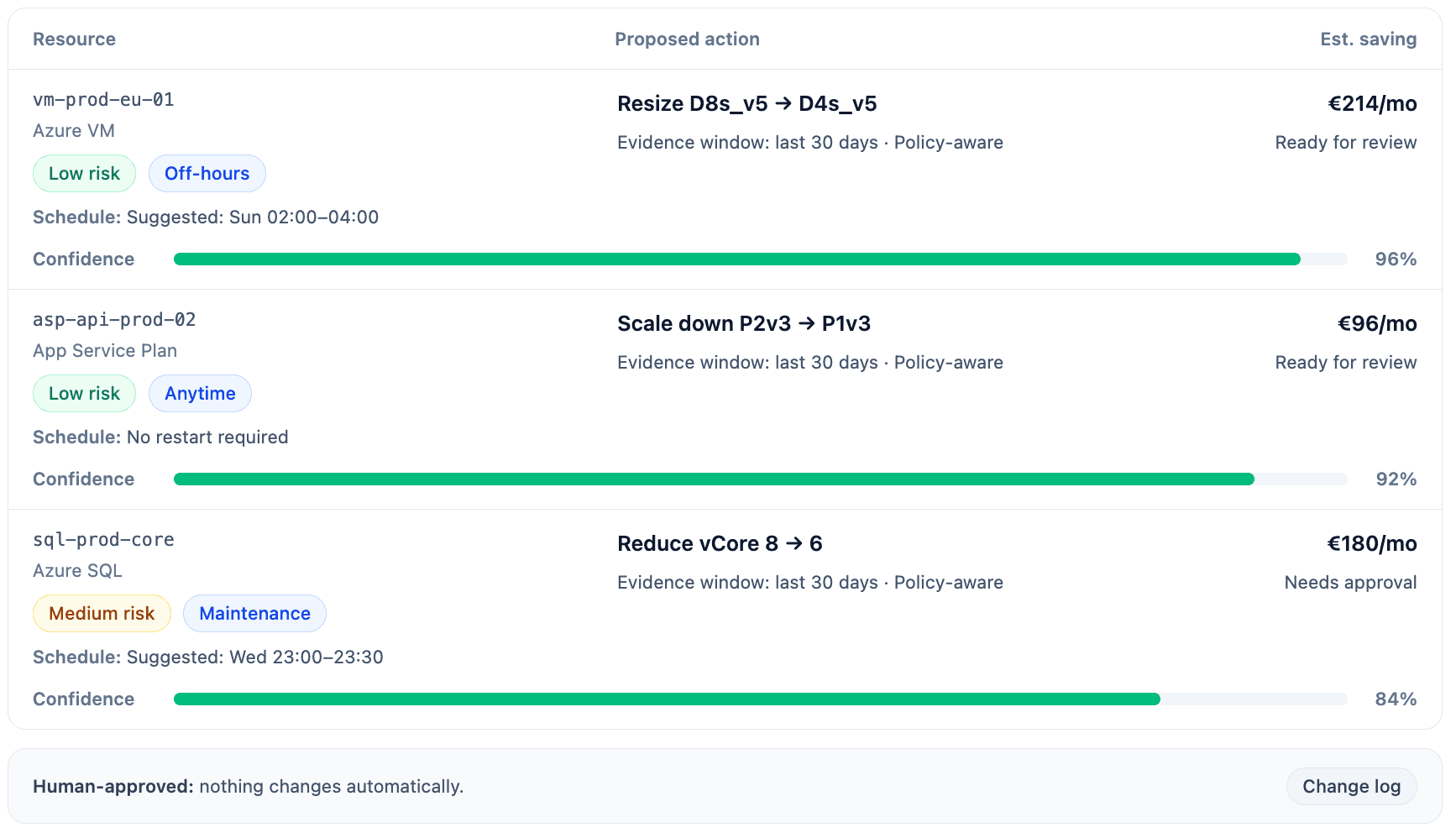
Prioritised queue with impact, risk, and evidence in one view.
Uses observed usage profiles (avg + tail behavior) and visible safety buffers.
Flags idle/orphaned resources with ownership and activity signals, not just “unused”.
Optimisation outcomes
Scan fast. Each outcome links to evidence.
Capacity recommendations based on observed usage profiles,not guesswork.
Detect waste with ownership and usage signals before proposing actions.
Spot consistent off-hours and propose safe runtime schedules.
Quantify savings and break-even, aligned to real utilisation.
Highlight savings opportunities while respecting policy and latency constraints.
Usage profiles and assumptions are explicit
Make risk visible: tail behavior, buffers.
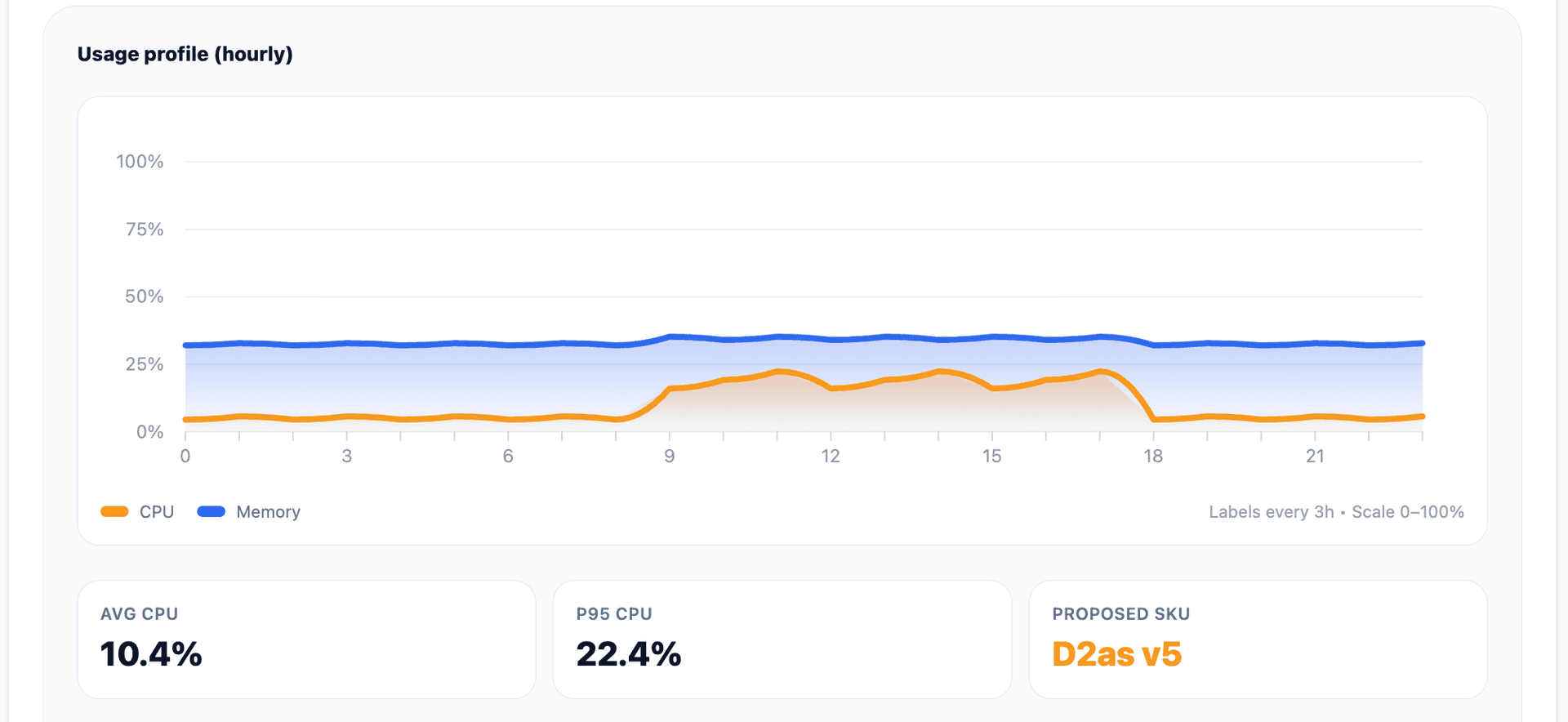
Metrics, tail behavior, buffers, and assumptions,explicit.
Every action includes the exact metrics, time windows, and stats used.
Avoids unsafe downgrades by checking constraints, features, and dependencies.
Safety headroom is visible (e.g., +X% buffer). No hidden heuristics.
Recommendations respect governance boundaries and can be audited later.
From data to safe action
A repeatable process teams can audit.
Collect usage signals per workload and environment.
Quantify impact and risk with transparent assumptions.
Start in read-only. Review evidence, assumptions,then decide what to approve.